In today’s connected world, security is a constant concern. Take for example the Office of Personnel Management (OPM) data breach in 2014, where personal information of an estimated 21.5 million individuals was stolen. The OPM performs background investigations into the suitability of individuals to hold government jobs and obtain security clearance.
If an organization that measures the trustworthiness of an individual is, itself, not trustworthy, what value does it have?
The challenge is that no single security solution is as good as it claims to be. You can’t buy a blinking box, or a piece of software and be secure. This is because without configuration, no one product can solve all your organization’s unique security needs, and because secure isn’t a finish line or a checklist. Today’s threat landscape is evolving rapidly, and a static security posture is simply insufficient. We must approach security as a process, a mindset, a way to view the world.
A changing model
Records indicate that OPM, which was breached in 2014, was woefully lax in all aspects of creating and maintaining a security program. Not only did they neglect to deploy basic technologies like multi-factor authentication and vulnerability discovery, they didn’t maintain a comprehensive inventory of their systems. Because their processes and technologies were outdated, they unilaterally failed to protect their data.
The rules for security are changing every day. The problem is that the old model of security was like an egg. Hard on the outside and soft on the inside. This model is based on several things that are no longer true.
The first out-dated assumption is that there’s a well defined and controlled perimeter between trusted devices (ones your organization owns and controls), and untrusted devices (everything else). However, more and more services are moving off-premise, whether to the cloud, to an offsite data center, or to any hybrid model. As a result, that well-defined perimeter becomes severely distorted. You can’t really define the perimeter anymore. And if you can’t define it, how can you defend it?
Think about it: Where is your perimeter? What’s inside it? Does it include your cloud hosting provider? What about your CEO’s iPad?
Another out-dated assumption is that you can trust the devices on your network. After all, they belong to the company, and have only company approved applications on them, right? Not really. With the degraded perimeter, and the advent of bring-your-own-device initiatives, “your devices” are often not yours anymore. They belong to your users, or your vendors. And if you can’t control them, you can’t trust them.
What’s next?
If you don’t control your network and you can’t trust your devices, what’s left? Have we lost the security battle?
No, not at all. We just have to change how we’re approaching the problem. Security is no longer about controlling devices and networks. A strong perimeter and tightly controlled devices were always about controlling access to your organization’s most valuable digital resource, data. With the decreased effectiveness of classic defense techniques, you need a more direct focus on controlling access to your data.
The risks to your organization are largely centered around your data. Where is it is located? How is it stored? Who has access? How is it sanitized for use in non-production environments?
To really understand what kinds of risks your organization faces, you have to understand what kinds of data you have, and what value that data has to attackers.
If an egg is the old model, the new model is an onion
Much like an onion, modern security practices are comprised of many layers of protection. Each layer gets more restrictive as you get closer and closer to your business critical data.
After the OPM breach in 2015, this document from the House Oversight Committee illustrates that CIOs at the federal level understood their responsibility at a whole new level.
Jason Chaffetz, Chairman, in a September 2016 letter to the House Committee on Oversight and Government Reform, states:
“The effectiveness of our country’s response depends on your answer to this question: Can you as the CIO be trusted with the highly personal, highly sensitive data on millions of Americans?”
Understand your data to understand your risk
When trying to get a better grasp on your data, here are some questions to ask:
- What kind of data do you have?
- Social Security Numbers
- Credit card information
- Other Personally Identifiable Information (PII)
- Who should have access?
- Staff
- Law enforcement
- The public
- What consequences can come from unauthorized access?
- Loss of PII
- Identity theft
- Credit card fraud
- Is the data at risk of unauthorized modification?
- Changing criminal records
- Issuing false warrants
- What would happen if the data is deleted or otherwise inaccessible?
- Deleting public records
- Site offline when needed
Once you’ve got a better understanding of your data, you can begin to model your risk, and from there, the steps you need to take to mitigate it.
A typical risk modeling and management cycle for your organization might look something like this:
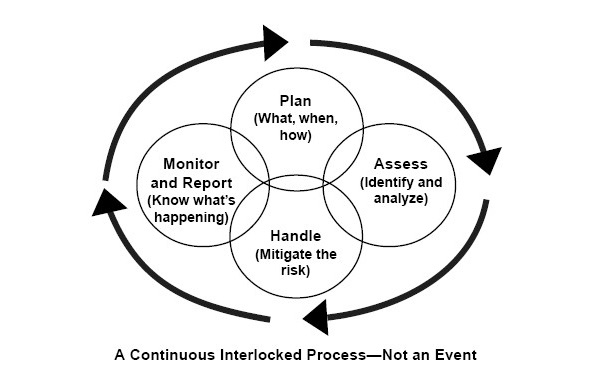
To begin the risk modeling process, you’ll want to ask the following questions about your data:
- How am I monitoring my environment?
- What am I going to do when a breach occurs?
- What data are my current risks?
- How am I going to mitigate these risks?
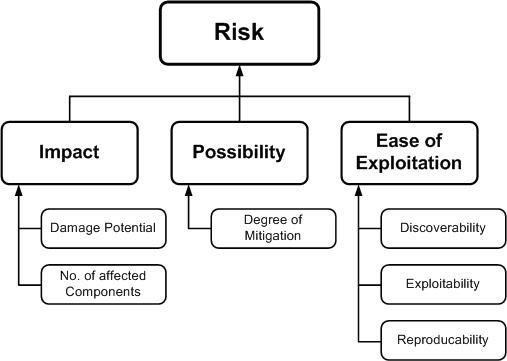
As you work on identifying your assets and analyzing the relative risk, here are some further questions to ask:
- What will be impact if this data is exposed?
- How likely is this to happen?
- How difficult would it be to access this data without proper authorization?
From there you can create an informed plan on how to secure your data. This includes how to monitor that security, and how to measure your success.
Turning things around
After their rather catastrophic breach in 2015, the OPM has made significant strides in strengthening their overall security posture. While many of the actions they’ve documented focus on the older, perimeter-centric, egg model, they also show an improved focus on the onion layers of risk evaluation and management. This includes incorporating important processes like security awareness training and multi-factor authentication.
OPM pursued these updated strategies as a reaction to an incident that has effected millions. The better option is to take proactive steps to improve processes and awareness before a breach can occur.
Security is an attitude
So, as you’re planning your next upgrade, move to the cloud, or a software purchase, please keep in mind that security is more complex than installing some software or purchasing an appliance. It’s an attitude that everyone in your organization must work together to embody. As with a chain, it only takes one weak link to undo otherwise excellent security.
To help you decide where to best spend your security budget and effort, the questions provided here are designed as a thought exercise to clarify your needs.
It’s not as overwhelming as it may seem if you know the right questions to ask. When thinking about securing your data, remember the old adage: Approach the task like eating an elephant…one byte at a time.
Author bio
In his career in SysAdmin and DevOps over the past decade, Lyle McKarns makes a point of asking the right questions about security to get the right answers. He also wins office cooking contests.